4th OSM Hackfest
Overview
ETSI's Centre for Testing and Interoperability and the OSM community organizied the 4th OSM Hackfest on 29 October to 2 November 2018.
The event was hosted by VMware in Palo Alto, during the OSM#6 meeting, offering a great opportunity to share and learn with OSM developers and module leaders, while getting hands-on experience with OSM Release FOUR
Participation to OSM Hackfests is free and open to all upon registration
Venue
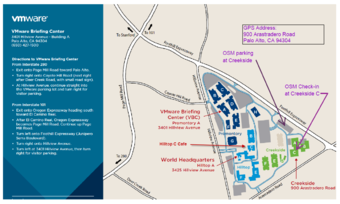
VMware Inc || Creeckside C
900 Arrastradero Road
Palo Alto 94304, CA, USA
Scope
This OSM Hackfest allowed new users to get familiar with OSM Rel FOUR and exercise all the main functionalities, from basic operations (installation, setup, common operations, etc.) to most advanced activities, with a big focus on VNF on-boarding activities covering Day 0/1/2 operations.
In addition, experienced users and developers had the opportunity to hack into OSM, fine-tune, test and demonstrate Rel FIVE and experimental features on the OSM Remote Labs network.
Objectives
- Install OSM and run some examples
- Get familiar with OSM's GUI and CLI
- Create your own VNF and NS descriptors and build packages
- Understand how to deploy NS/VNF with EPA
- Learn how to add dynamic LCM with Day-1 and Day-2 actions with charms
- Basic troubleshooting
- Freestyle Experimental Sessions
Who attended
- VNF vendors, who want to onboard their VNF in OSM following best practices
- System Integrators, who want to get used with OSM
- Service providers, who want to get first hand operational experience with OSM
- Academia and Universities, who are considering OSM as platform for their research activities in networking
- Experimented developers and users that want to share and test with the community
Prerequisites
- Sits are limited, registration is mandatory
- Laptop / VM in laptop
- Linux installed (preferred, Ubuntu 16.04)
- RECOMMENDED: 2 CPUs, 8 GB RAM, 20GB disk
- User-level knowledge of Linux
- Familiarity with NFV and SDN concepts
- For optimal use of the time it is highly recommended that you download and install the OSM Rel FOUR vagrant image (including virtualbox and vagrant) prior to the hackfest. Please see https://osm.etsi.org/wikipub/index.php/How_to_run_OSM_on_Vagrant for details on how to download and install OSM on your computer.
Agenda
- Session 0: Introduction to NFV and OSM
- Session 1: OSM Installation and first use
- OSM installation (Release FOUR)
- OSM user experience from the UI
- OSM user experience from the client
- Session 2: Creating a basic VNF and NS
- Tutorial. Creating descriptors and packages (simple VNF - single VM, no EPA, no charms)
- Hands-on session.
- Session 3: Modeling multi-VDU VNF
- Tutorial. Creating descriptors and packages (complex VNF - multi-VDU)
- Hands-on session.
- Session 4: Adding day-0 configuration to your VNF
- Tutorial. Creating descriptors and packages (complex VNF - multi-VDU, day-0 config via cloud-init, no charms yet)
- Hands-on session.
- Session 5: Modeling EPA capabilities in your VNF descriptor
- Tutorial. Creating descriptors and packages (complex VNF - multi-VDU, day-0 config via cloud-init, EPA, no charms yet)
- Hands-on session.
- Session 6: OSM Fault & Performance Management
- Tutorial. Collecting and visualizing metrics from VNFs
- Hands-on session.
- Tutorial. Collecting, visualizing and reacting to events from VNFs
- Hands-on session.
- Session 7a: Adding day-1/day-2 configuration to your VNF. Creating a charm for your VNF
- Session 7b: Adding Charms to your VNF Descriptor
- Tutorial. Introduction to VNF Package Generation and VNF Primitives
- Tutorial. Creating a charm for a VNF (SSH access and execution of a command)
- Hands-on sessions.
- Freestyle Experimental Sessions
- Session 7c: Charms Exercises
- Experimenting with SFC (hands-on session, details at Pad)
Instructors
- Benjamín Díaz, Whitestack
- Eduardo Sousa, Whitestack
- José Miguel Guzmán, Whitestack
- Additional Support from:
- Pankaj Varade, VMWare
- Gianpietro Lavado, Whitestack
Remote Labs
OSM Hackfests rely on exercising OSM with different VIMs and infrastructure in Remote OSM Labs kindly made available by our community members. Special thanks to the ones supporting this hackfest :
- Intel
- VMware
- Whitestack
- Wind River
Hackfest material
Previous Hackfests material
Get involved
- Join the OSM Community Slack Workspace
- If your organisation is already an OSM member, you can also:
- Request an EOL account (if you don’t have one yet)
- Subscribe OSM general and OSM TECH mailing lists
- If your organisation is not yet an OSM member:
- Learn how to join, it is free and open to all
- Join the OSM Ecosystem
Contact
Please send your technical questions to OSM_TECH@list.etsi.org or join the OSM Community Slack Workspace
Questions about ETSI, joining OSM, this hackfest and future events can be sent to: OSMSupport@etsi.org